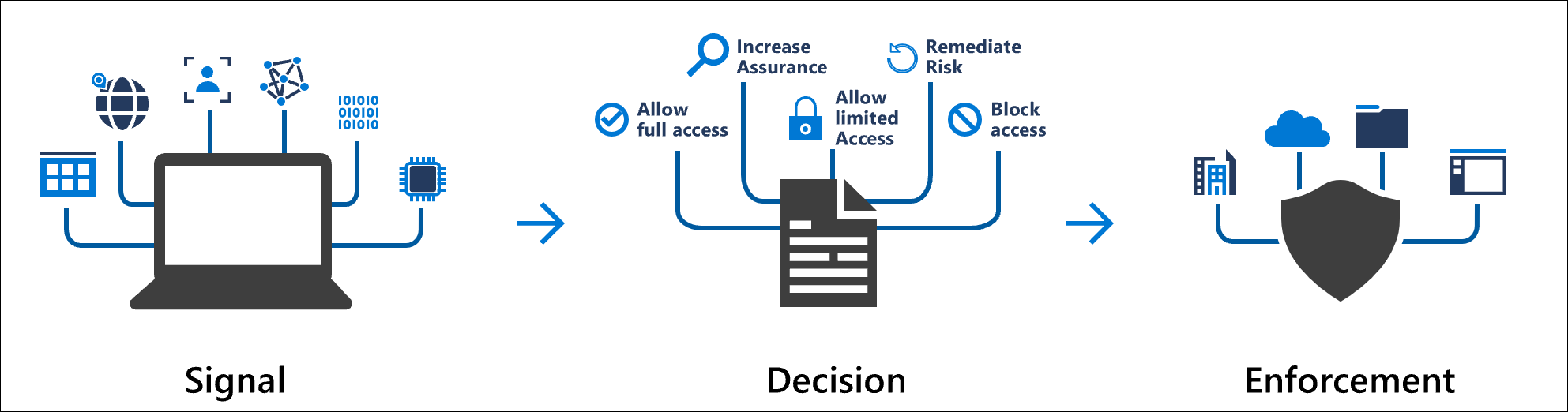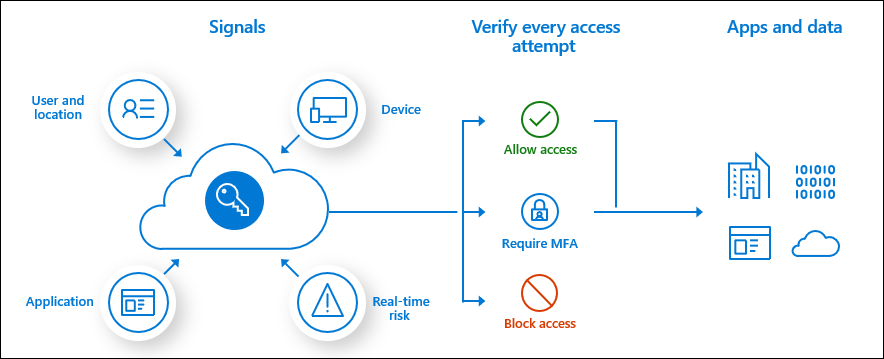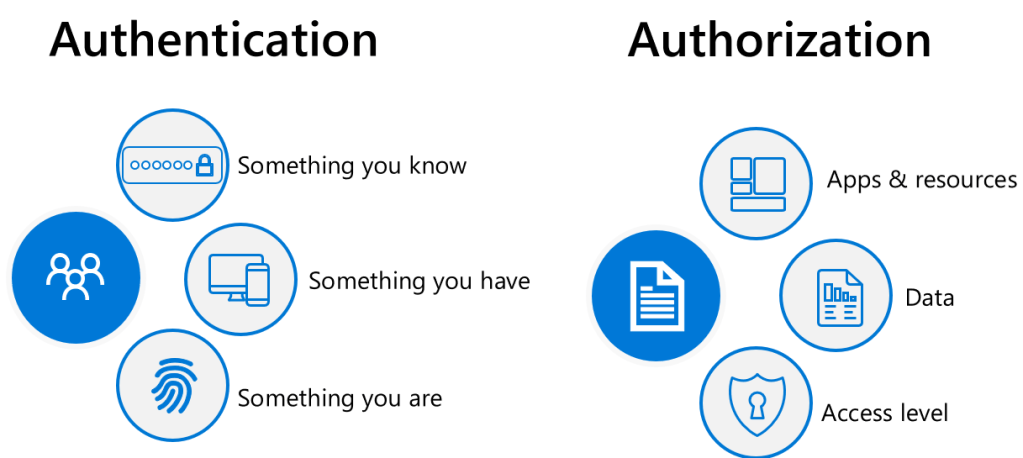
The image above is a high level overview of all identity protection methods regardless of vendor and especially when it comes to implementing Zero Trust. A lot of organisations do not really know what Zero Trust is, or how to begin their Zero Trust journey.
Zero Trust is a bit like Data Classification, it becomes an operational task that will never end. It is not implemented as a project but more as an operational procedure, that constantly evolves as threats and data protection requirements evolve. I have not yet seen a Zero Trust request from an organisation yet that are exactly the same. Zero Trust strategies can often be similar per industry like , legal, pharma, manufacturing and food industry etc..
The purpose of this blog post is to show how Azure Identity Protection and Microsoft Defender for Identity protection work together and can improve any organisation’s security posture as Identity is the new security plane and the days of protecting identity behind edge perimeter firewalls are no longer relevant.
Not all organisations’ (like SMB) can afford Microsoft Azure Identity Protection. I normally advise SMB organisations to procure Azure AD Premium plan 2 licenses to protect any privileged accounts.
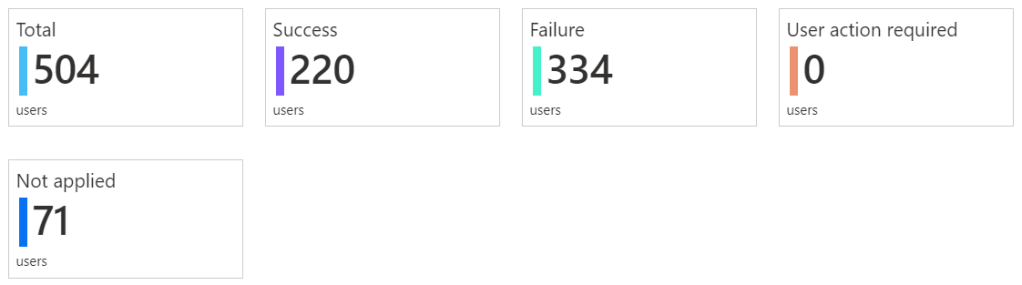
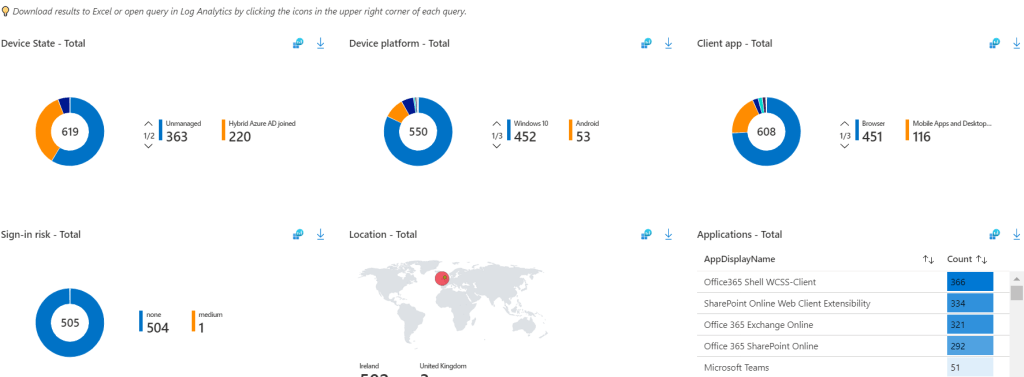
For enterprise organisations that are licensed for Azure Identity protection, my preference for implementing the Azure Identity Protection controls, is via Conditional Access. This provides additional insights when placing the policies in report mode only and then reviewing the reports in Conditional Access – Insights and Reporting.
Azure Active Directory Topology

The image above illustrates Azure ADDS (Active Directory Domain Services) and Azure AD. So, think of Azure Identity Protection, as a service protecting identity at the cloud level or like the traditional perimeter edge firewall for ADDS. Microsoft Defender for Identity, protects on-premise identities.
Microsoft Azure Identity Protection
Identity Protection is a tool that allows organizations to accomplish three key tasks:
- Automate the detection and remediation of identity-based risks.
- Investigate risks using data in the portal.
- Export risk detection data to your SIEM.
Identity Protection uses the learnings Microsoft has acquired from their position in organizations with Azure AD, the consumer space with Microsoft Accounts, and in gaming with Xbox to protect your users. Microsoft analyses 6.5 trillion signals per day to identify and protect customers from threats
Microsoft Defender for Identity
Microsoft Defender for Identity monitors domain controllers by capturing and parsing network traffic and leveraging Windows events directly from domain controllers, then analyses the data for attacks and threats. Utilizing profiling, deterministic detection, machine learning, and behavioural algorithms Defender for Identity learns about your network, enables detection of anomalies, and warns you of suspicious activities.

Microsoft Defender for Identity provides alerts to suspicious lateral movements in an on-premise network with ADDS identities. The alerts are great but can only be actioned as soon as a Security staff member can respond to the alerts.
The two automated responses that Microsoft for Identity can perform are:
Disable user – this will temporarily prevent a user from logging in to the network. This can help prevent compromised users from moving laterally and attempting to exfiltrate data or further compromise the network.
Reset user password – this will prompt the user to change their password on the next logon, ensuring that this account cannot be used for further impersonation attempts.
Typically, all enterprise organisation’s do not permit internet access on their domain controllers, except for port 53 (DNS) or port 123 (Network Time Protocol), but most normally domain controllers internet connectivity is controlled by proxies
The Azure AD Premium P1 and P2 password protection service, provides an excellent topology. An agent is installed on domain controllers that then communicates with a proxy agent installed on a server, that has internet access, like an AD connect server.
Microsoft Defender for Identity standalone sensor
The standalone sensor requires two network adapters.
1: Management Adapter: used for communications on your corporate network
2: Capture adapter: used to capture traffic to and from the domain controllers
The below ports are required to be configured for standalone sensor

Azure Sentinel
Playbooks may be available in the future that can perform more automated remediation tasks with Microsoft Defender for Identity.
Microsoft have provided an online demonstration on how to compromise an identity and take control of a domain, which I find hard to believe, however, it is a bit like ethical hacking. Security professionals must know the lateral movements of a bad actor when attempting to compromise an identity and an on-premise Active Directory domain.
The article is available HERE
Microsoft Defender for Identity also provides some recommendations, when the Microsoft for Defender Identity sensors (agents) have gathered telemetry information on an on-premise Active Directory instance. An example would be ‘implement secure LDAP’, when an organisation reviews the recommendations provided by Microsoft Defender for Identity, some careful planning is required to assess the impact of implementing the recommendations that Microsoft Defender for Identity has provided.
When Azure Identity Protection and Microsoft Defender for Identity, has been fully implemented in an organisation, it will really improve the organisation’s security posture and Microsoft will continually develop these services to protect against existing and future vulnerabilities.