In my previous post on how to secure Office 365 Roles and this post is about how to secure Azure Resources.
Office365 and Azure Active Directory have a number of roles that are familiar like global administrator , compliance administrator etc. One of the most common use cases for Azure PIM it to request just in time access to the global administrator role
As organisations extend their networks into Azure , Azure subscription’s costs can sometimes spiral out of control. And this post will demonstrate the technical steps required to lock down the ‘virtual machine contributor’ role with Azure Privileged Identity Management, so that it requires finance department or senior it approval to create virtual machines in Azure, and the process around making technical admin staff eligible for the ‘virtual machine contributor role’
An example of how Azure costs could spiral , An Azure Admin , provisions the most expensive high performance virtual machine available in Azure, makes the VM geo-redundant, adds in a few ultra disks and a few Terra Bytes of Azure Blob Strage.
If there are multiple Azure subscriptions, The eligible users and app-rovers will need to be configured per subscription.In the image below we want to manage Azure Resources.
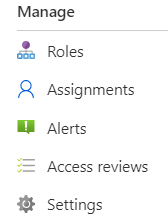
 We click on Azure Resources and then click on settings.
We click on Azure Resources and then click on settings.
Add the app-rovers for the role and ensure the app-rovers have mailboxes so that they receive the email notification
 Next step is to add eligible users for the virtual machine contributor role.
Next step is to add eligible users for the virtual machine contributor role.
 Now any admin that needs to provision a virtual machine in Azure has to follow a workflow and can only do so when senior IT resources or finance department users have approved the provision of the virtual machine
Now any admin that needs to provision a virtual machine in Azure has to follow a workflow and can only do so when senior IT resources or finance department users have approved the provision of the virtual machine




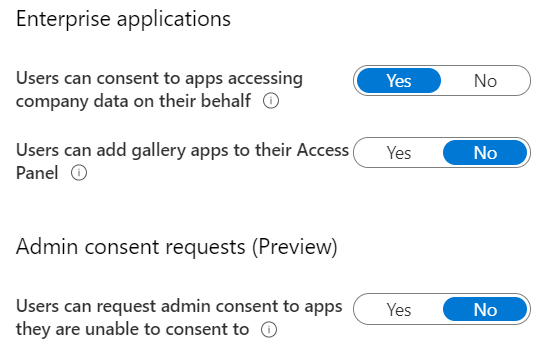
 Application administrators should be granted the application administrator role in Azure Active Directory , Then the next time an and user wants to add an application, the application administrator will receive an email and can approve from his\her Outlook client.
Application administrators should be granted the application administrator role in Azure Active Directory , Then the next time an and user wants to add an application, the application administrator will receive an email and can approve from his\her Outlook client.
 Next change target domain to contoso.com or a fqdn of a domain controller in contoso.com
Next change target domain to contoso.com or a fqdn of a domain controller in contoso.com Finally stop and start the synchronization task.
Finally stop and start the synchronization task.







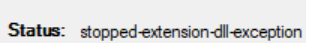
 I started to notice that Azure AD connect was failing and had a look in the console and seen the error message in the console displayed in the image below
I started to notice that Azure AD connect was failing and had a look in the console and seen the error message in the console displayed in the image below